Office 365 is one of the most popular sets of subscription suites for productivity software used at the corporate level.
The compatibility to a wide spectrum of operating systems and the variety of programs available on Office, make it an obvious choices for many medium size to large businesses.
Weak Links in the Chain
Office comes with its vulnerabilities, however.
The fact that Office 365 is an online platform, means that applications are accessed via an internet portal and data such as company email, is stored on a cloud server. This opens the possibility for hackers to target Office user accounts, potentially gaining unauthorized access to company projects and client communications.
Unfortunately, Office in this way is a victim of its own success.
Because of its popularity among large businesses, Office 365 has become a major focus of cybercriminals, with attacks against the platform increasing 600 percent over 2016.
Indeed, Office’s creators at Microsoft, understanding the vulnerability posed by keeping so much sensitive data accessible through a single portal, applied the two factor authentication on its Azure cloud service to securing the Office suite accounts.
Azure multi-factor authentication (MFA) protection is less than ideal, however.
The authentication settings on Azure give a user a number of options. These include the pretty standard methods of SMS and hard token delivered pin numbers. Both of these methods carry significant drawbacks, from both a security, as well as user-experience perspective. SMS authentication has been depreciated as more and more methods in hacker interception are being discovered. As far as tokens are concerned, software versions pose some of the very same vulnerabilities as SMS, while hard-tokens require users to carry and safeguard an additional device, closing one security gap while opening another.
The potential failings of Azure’s security has become manifest in a number of data breaches including the most recent incident involving Deloitte one of the world’s “big four” accountancy firms. In late September, the company disclosed that a slew of client communications stored on Azure servers were accessed by hackers during an email migration shifting to Office 365.
Internal Flaws in Office365
Office 365 also faces threats from within.
Due to the complexity of the suite, and the fact that many earlier Microsoft products have been embedded in the current applications, program flaws are regularly discovered in Office 365. Many of these flaws are the basis for serious security compromises. One widely circulated incident serves as a poignant example: In the Summer of 2016, hackers were able to exploit a zero-day flaw in the suite that allowed ransomware embedded in a Word file to go undetected by Office security measures. According to Microsoft, some 18.2 million Office 365 subscribers were affected before the flaw was able to be patched.
This revelation of flaws in Office security protocols lead many industry leaders to consider options for bolstering illicit access detection on the platform. If bugs exist that allow malware to go undetected on Office, what could that mean for unauthorized access protection?
See how the authentication process work Using the Octopus Authenticator
Circumventing the Threats
Securing user identity for Office 365 and other online suites requires a solution that can circumvent all of the typical weaknesses associated with multi-factor authentication methods.
Keyless authentication technology of Secret Double Octopus allows strong authentication with both flexibility and seamless user experience.
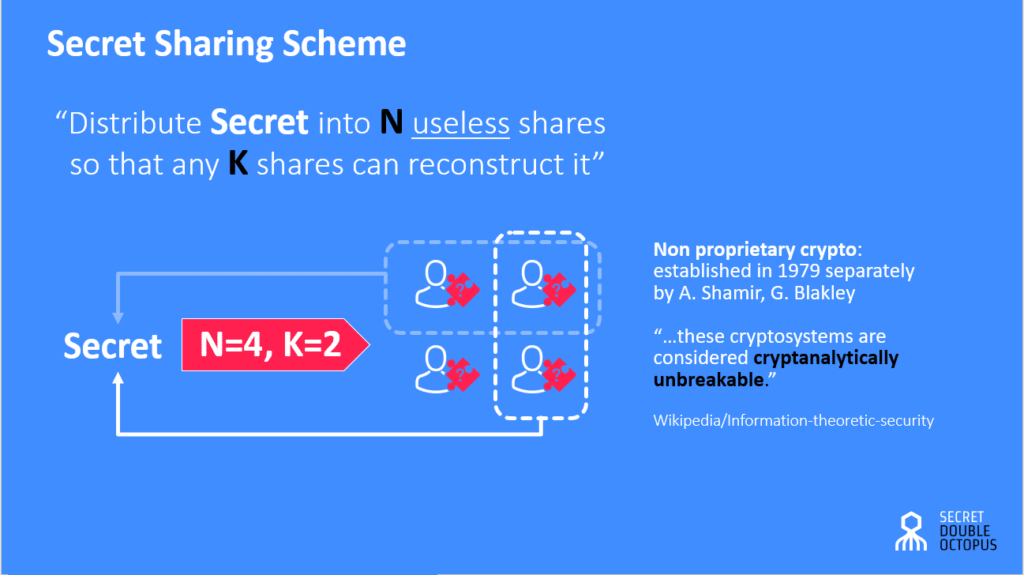
The Octopus Authenticator works by incorporating the mathematically unbreakable “secret sharing” algorithm to authentication information, splitting the data into several pieces. Each data fragment, or “share”, is useless on its own if intercepted. The shares are then transmitted via multiple secure channels. Cybercriminals would have to overcome the defenses of each channel simultaneously in order to hack the system. On the user’s end, all that is required is the tap of a mobile push notification. By eliminating the need for passwords and other traditional authentication methods, the Octopus Authenticator keeps the authentication process easy and smooth.