What is Passwordless Authentication?
Passwordless authentication is any method of verifying the identity of a user that does not require the user to provide a password.
Instead of passwords, proof of identity can be done based on possession of something that uniquely identifies the user (e.g. a one-time password generator, a registered mobile device, or a hardware token), or the user’s biometric signature (e.g. fingerprint, face, retinal scan, etc.). It is also possible to authenticate based on something the user knows (e.g. knowledge-based authentication), so long as that something is not a password.
Why Do We Need Passwordless Authentication?
Passwords have been a sore problem for businesses from the very beginning.
At RSA’s 2004 security conference, Microsoft founder Bill Gates predicted “There is no doubt that over time, people are going to rely less and less on passwords,” adding that passwords “just don’t meet the challenge for anything you really want to secure.” And yet in 2017 according to Verizon research 81% of breaches were attributed to stolen credentials, a stark reminder of just how common passwords still are–and the damage they continue to cause.
A pertinent truth that is often forgotten when discussing the importance of authentication is that passwords should have been removed from the equation a long time ago. We have–and have had for some time–the technology for much more viable alternatives.
How Does Passwordless Authentication Work?
Passwordless authentication can work through a variety of different authentication and encryption protocols. But the defining element of all passwordless solutions is that authentication credentials are never fixed within the system, rather new authentication data is generated at the beginning of every session. It is this crucial element that gives passwordless solutions their security advantage.

What Types of Passwordless Authentication are There?
As alluded to above, authentication methods in general can be divided into three broad categories: Something the user has (such as a hardware token), something the user is (i.e. biometric data), and something the users knows.
The password alternatives available on the market today are represented in all three of those categories and cover a pretty broad spectrum. These system types include:
- Software tokens
- Biometric scanners
- SMS delivered codes
- Hardware authentication devices (“hard” tokens)
While they are certainly better than nothing, all of these platforms have been shown to possess serious vulnerabilities.
From a security perspective, the strongest passwordless solutions consist of multi-channel and out-of-band authentication mechanisms. This feature is what makes Secret Double Octopus’s technology based on the mathematically unbreakable Secret Sharing scheme, resilient to the full range of known attacks.
What Are The Benefits of Passwordless Authentication?
- User Experience (UX): passwordless authentication means no more user memorized secrets, streamline the authentication process
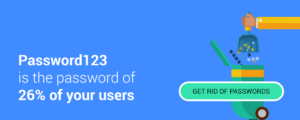
- Better Security: User controlled passwords are a major vulnerability, users reuse passwords, are able to share them with others. Passwords are the biggest attack vector and are responsible for %81 of breaches, they also lead to attacks such as credentials stuffing, corporate account takeover (CATO) Password Spraying, brute force attack
- Reduction in Total Cost of Ownership (TCO) : Passwords are expensive, they require constant maintenance from IT staffs, removing passwords will reduce support tickets and free IT to deal with real problems
- IT Gains Control and Visibility: Phishing, reuse, and sharing are common issues when relying on passwords, with passwordless authentication IT reclaims its purpose of having complete visibility over identity and access management – Nothing to phish, share or reuse, the user is no longer the wild card in the organization identity scheme.
What Type of Attacks Does Passwordless Authentication Prevent?
Passwordless solutions help prevent all attacks that take advantages of the inherent weaknesses in password authentication, such as sophisticated guessing mechanisms as well as methods that get between authenticated users and servers to intercept communications. These include:
- Credential stuffing
- Password spraying
- Man in the middle attack
- Phishing and Spear Phishing
- Mimikatz
- Rainbow Table
- Pass the Hash
- Corporate Account Takeover (CATO)
- Dictionary Attack
- Meterpeter
What other non-security benefits can passwordless authentication add?
Beyond improving security posture, passwordless systems can offer companies important operational benefits as well.
User experience – UX – is one such benefit. Removing passwords from the picture means users no longer have to devise and remember a password for each of their accounts. Nor do they have to type them in every time they log on to one of those accounts.
No passwords also means cutting the costs of maintaining and administering them. According to industry research, password resets account for as much as half of all help desk calls, which places a tremendous burden on company IT. According to Forrester, the cost of a single password reset averages $70.
Is Passwordless Authentication Compliant With Regulatory Standards?
In the past years, regulatory bodies have come to understand and acknowledge the weaknesses and security threats associated with the storage and use of passwords. That’s why they’re constantly raising the bar for the minimum requirements of passwords (length, complexity, encryption, change cycles) as well as making it mandatory to add two-factor authentication in many settings.
The NIST, the body that sets technology standards in the U.S. and acts as a point of reference for many other countries, requires that in many settings services secure user identities through multi-factor authentication (MFA). This means the service must support at least two of the following:
- Something you know (password/username)
- Something you have (mobile device or FIDO key)
- Something you are (biometric data)
In some settings, such as financial service, the standards body explicitly requires the use of biometric data as one of the authentication factors. This means that a technology such as Secret Double Octopus, which combines out-of-band mobile and biometric authentication, is a good choice to make sure your organization is compliant with security standards and regulations while also using convenient, user-friendly technology.
Can Passwordless Solution be Implemented in a Hybrid Enterprise (cloud/on-premises)?
Yes. Due to the increase in the integration of on-premises and cloud-based identity management systems, many authentication solutions have adapted themselves to this model.
The Octopus Authenticator is fully integratable with network services such as Microsoft’s Active Directory and other cloud platforms making it a suitable solution for hybrid enterprise.
If I Already have a Second Authentication Factor how will a Passwordless Solution Help?
Many organizations use a second factor on top of passwords to beef up their security. Unfortunately, this is essentially a band aid approach. A password-plus-second-factor policy still has the inherent flaws of passwords; users are still required to memorize and safeguard secrets, the security risk of password reuse still exists, and the costs of maintaining passwords also remain. Even the additional layer of assurance administrators get from a second factor is undermind when passwords are still part of the equation. As recently revealed by researchers at Proofpoint, passwords can be leveraged using legacy protocols such as IMAP to bypass second factors and gain illicit access to accounts.
Can any Application Utilize Passwordless Authentication?
While many applications rolling out from developers are passwordless compatible, comprehensive support for a full set of passwordless options is only just starting to become a trend within the world of IT.
Some industry leaders have been experimenting with methods for cross-platform integration of passwordless systems. Secret Double Octopus’ provides solutions for integrating advanced authentication into existing as well as new apps making sure all business applications are passwordless, from cloud applications to legacy software.
Secret Double Octopus – Passwordless Authentication Process