Large tech companies like Microsoft and Google go to great lengths to secure their services and protect their customers’ accounts and identities. But what about the security of the partners and third parties that provide services on their behalf?
A recent article on famous cybersecurity blog KrebsOnSecurity blog post unveiled a breach at PCM, a major California-based provider of technology products, services, and solutions, and also a Microsoft partner. According to sources, after breaching the systems of PCM, attackers were able to gain access to the “administrative credentials” PCM uses to manage client accounts in Microsoft’s Office 365.
Damages that are not too minimal
According to reports, attackers were primarily interested in stealing information that could be used to conduct gift card fraud at various retailers and financial institutions. In an official statement, PCM tried to downplay the incident, explaining that the breach exposed “minimal” customer information and the affected customers were immediately contacted.
But this was, in fact, a very dangerous breach, and while we don’t know the extent of activities the attackers carried out, the damage could have been much worse. PCM’s customers include businesses as well as state and federal governments, which means the company was responsible for managing sensitive accounts.
According to Robert Prigge, President of mobile payment service Jumio, there’s nothing “minimal” about the information stolen during the PCM hack. “Having your personal email hacked is one thing (not to understate the plight of identity theft victims), but having the administrative credentials stolen from PCM – the same credentials they use to manage client accounts within Office 365 – is next level,” Prigge says.
The need for strong multi-factor authentication
The PCM hack is yet another reminder that IT security teams must win every time—hackers only need to win once. Cloud providers like PCM, which oversee vast amounts of resources for many clients, will continue to be an attractive target for cybercriminals, who prefer to hit the safe rather than pick the pocket of individual users.
Shortly after the PCM intrusion, Microsoft published new rules and guidelines for its partnership programs, requiring “partners who are participating in the Cloud Solution Provider program, Control Panel Vendors, and Advisor partners” to enforce “Multi-Factor Authentication (MFA) for each user, including service accounts.”
Microsoft made it mandatory to implement MFA for key administrative roles, which it calls “the most privileged Azure Active Directory roles”. The roles include:
- Global administrator
- SharePoint administrator
- Exchange administrator
- Conditional access administrator
- Security administrator
- Helpdesk administrator / Password administrator
- Billing administrator
- User administrator
According to a Microsoft statement, the administrators for these nine types of accounts will need to perform MFA every time they sign-in.
MFA is the process of verifying users’ identities in multiple steps. For instance, in addition to providing the password to their accounts, users will be required to produce a biometric challenge (e.g., fingerprint or face scan) or type in a one-time passcode (OTP) sent to their mobile device.
Multi-factor authentication considerably reduces the risks of data breaches. Even if cybercriminals obtain usernames and passwords, they won’t be able to access the accounts without producing extra proof of ownership.
PCM is just one of several cloud IT providers that have fallen victim to data breaches in the past few months. Earlier this year, IT outsourcing giant Wipro suffered a massive breach, which affected many customers. Again, the lack of proper authentication mechanisms came at a huge cost to the company—and its business customers.
So what are the main takeaways? First, there should be no compromise on the security of administrative accounts and resources. Any administrative access should absolutely be protected by MFA. But even for less sensitive accounts, passwords should never remain the only factor for authentication.
Finally, when businesses want to outsource the administration of their online resources, MFA should be a non-negotiable requirement from your cloud provider. If an IT company can’t guarantee the security of your administrative accounts, then they’re not qualified to manage data on your behalf.
Passwordless MFA is the true solution
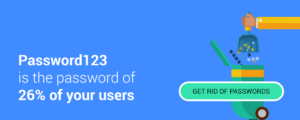
Multi-Factor Authentication (MFA) has existed for a long time, but organizations struggle to implement it in the right way. The problem is that MFA often introduces friction and degrades the user experience. Users don’t like complicated, multi-step login processes, especially when they have to log in frequently. This often puts off users and pushes them toward turning off MFA or circumventing it.
Passwordless MFA solves the problem by providing a solution that is both secure and easy to use. Removing passwords from the authentication process is beneficial to both users and service providers. Users are relieved of the difficulties of creating, memorizing and changing long and complex passwords. Service providers are relieved of the pains and concerns of storing and securing user secrets. And when you don’t have a large cache of user passwords, hackers have less incentive to attack you.
An example of passwordless MFA is Secret Double Octopus, which is compatible with many popular on-premise and cloud services. Secret Double Octopus replaces passwords with a multi-channel authentication system that is both secure and easy to use. Users simply install the Octopus Authenticator app on their mobile device. Logging in is a simple touch-and-go experience. Under the hood, a highly secure authentication process takes place.
In the world of cybersecurity, there’s no such thing as “absolute security.” But you still must do everything you can to minimize risks. In this regard, getting started with passwordless MFA is a critical first step.