The EU’s new General Data Protection Regulations (GDPR) will come into effect in less than a year.
From next May, a slew of new legal protocols will come into effect. These will include, mandatory fines along with mandatory breach notifications, where a company has less than 72 hours after they become aware of a data breach to notify its customers.
Let’s look at what are the latest and most significant changes, what a CIO or CSO needs to know about them, and what companies should consider changing in their security apparatus to become compliant.
So what are the important changes?
The newest additions to GDPR include two things:
- The right to be forgotten, whereby subjects can ask to have their personal data removed under certain circumstances.
- The right to have consent for your data to be used for specific purposes, rather than just clicking on a site’s privacy policy splash screen to give the site carte blanche access.
What the Security Officers Need to Know
What this means is the way organizations collect sensitive data might need review and rethinking. Companies will have to be more transparent about the type of data they collect on individuals, how that data is used, and when personal information is exposed in a breach.
The bottom line:
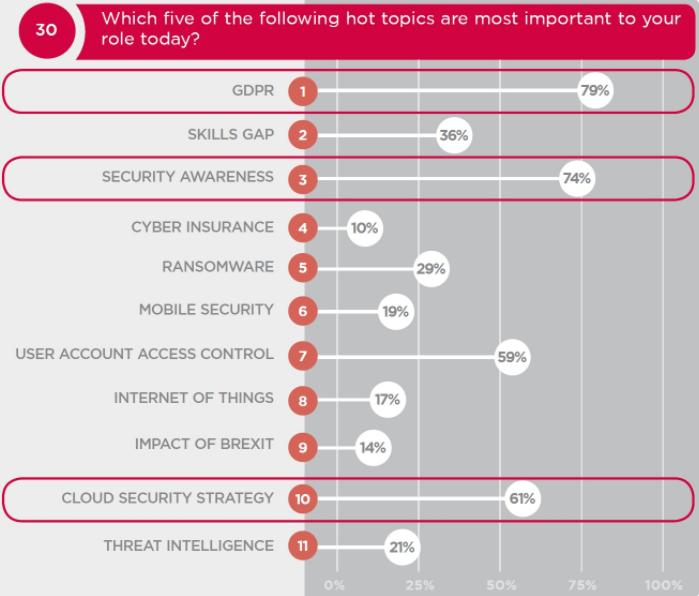
GDPR is a major concern for CISO’s, according to their own testimony presented in the graph below.
While the regs do not explicitly outlaw authentication with only username and a static password, there will be trouble if your enterprise continues to make use of these weak types of protection and authentication of your users’ sensitive information.
For many organizations, the weak link in the chain is the password and more specifically how people use them. We all know those password horror stories, yet many of us continue to reuse passwords, or write them down, or both.
Let’s use the coming of GDPR as a clarion call to change this behavior.
Changes to Come
One big change would be to start redrawing some of your authentication technologies and to strengthen how you authenticate your users.
Smart organizations are looking to use the technology-refresh opportunity to get rid of passwords completely. As you plan your GDPR approach, look to eliminate passwords and move instead to solutions that deliver more convenient and secure options for your users.
Big players in the IT world have already begun to issue advisories on how to navigate the technicalities of GDPR
Microsoft for instance has recently produced a collection of GDPR assuagement tools including sample PowerPoint presentations, Excel/PowerBI workbooks and other aids that can help your internal IT staff put together your own plan.
What you should take away from this post is that there is no magic bullet to become GDPR compliant. It is a process, not a destination, a series of both small and big steps. Understanding the implications for your particular circumstances will require careful study.