FIDO Authentication and the Shift Towards Passwordless Security
Adding multi-factor authentication (MFA) to password logins hasn’t slowed phishing attacks that lead to ransomware and data loss. More security awareness training can’t stop it either. And, while the dream of passwordless dates back many years, it seems like we’re finally moving closer to realizing an end to the password and phishing menace.
What You Will Learn:
- The role of FIDO Authentication in advancing (MFA)
- The concept, protocols, and implementation strategies of FIDO Authentication
- The two types of passkeys
- FIDO limitation for workforce MFA
- How Octopus extends FIDO usability with enterprise-wide use case coverage
The FIDO Alliance, an open industry association focused on reducing the world’s overreliance on passwords, has taken a big step toward phishing resistance. The alliance is tasked with creating an authentication standard that can be adopted by all organizations worldwide.
FIDO, which stands for Fast Identity Online, is a set of open technical standards that establish user authentication methods to reduce reliance on passwords. Many more companies joined the alliance, including tech giants Google, Microsoft, Apple, and Amazon. FIDO also counts large hardware manufacturers like Intel, Apple, and Samsung among its members, as well as several financial institutions such as Visa, MasterCard, and American Express.
But for all the star power, implementing FIDO proves challenging for most enterprises.

Making sense of the confusing FIDO specifications
Over the years, the FIDO Alliance has developed a number of different standards and specifications, some of which build upon each other. The terminology can be a bit confusing to the uninitiated. Here’s a quick breakdown of what you need to know:
What is FIDO?
The first FIDO specification, published in December 2014, included two components: The Universal Authentication Framework (UAF) and the Universal 2nd Factor (U2F).
U2F is the standard for physical security keys that act as a second factor (2FA) to the passwords of your online accounts. U2F keys are usually connected to your computer via USB, but there are also near-field communication (NFC) and Bluetooth Low Energy (BLE) models that can be used for mobile devices. U2F devices use the public encryption key scheme to protect your account. The private key is stored exclusively on the U2F device and never leaves it, which makes it much more secure than SMS- and time-based 2FA methods that can be spoofed by crafty hackers.
The UAF protocol is a standard that allows services to adopt passwordless and multi-factor security. When creating accounts, users register a device of their choice with the service and specify a local authentication mechanism such as fingerprint scanning, facial or voice recognition, entering a PIN, etc. As U2F, UAF creates a key pair, stores the private key on the device and the public key in the service’s servers.
Whenever users want to log into a UAF service, instead of typing a password, they just need to repeat the UAF method they had signed up with, such as running a fingerprint scan on their device.
What is FIDO2?
In April 2018, the alliance launched FIDO2, an updated and upgraded version of its original specifications. FIDO2 was meant to facilitate the adoption of secure, passwordless authentication for a wide range of online services and user devices.
The main component of FIDO2 is Web Authentication (WebAuthn), developed in collaboration with the World Wide Web Consortium (W3C). WebAuthn is a set of standards and web application programming interfaces (APIs) that can add FIDO-based authentication to supported browsers and platforms. This means users will be able to log into their favorite mobile and web applications using biometrics, mobile apps or FIDO keys.
WebAuthn was meant to make FIDO authentication more accessible to users who use various technologies. The standard is supported by all popular browsers, including Chrome, Firefox, Edge, and Safari. Windows 10 and Android also provide native support for WebAuthn. The alliance provides a status page that follows the implementation of WebAuthn in popular browsers.
With the advent of FIDO2, the alliance retained the U2F standard but relabeled it as Client to Authenticator Protocol (CTAP1).
In the same release, FIDO also introduced CTAP2, which is basically the same as U2F but relaxes its requirements to also include mobile devices as acceptable external authenticators.
Key features
- FIDO 1.0:
- U2F/CTAP1: Standard specifications for physical two-factor authentication (2FA) keys
- UAF: Standard specifications for passwordless authentication technologies
- FIDO 2.0:
- WebAuthn: A standard set of web APIs to allow passwordless authentication in browsers
- CTAP2: Specification for the usage of physical keys and mobile authenticator apps to implement 2FA and passwordless authentication
What is passkey?
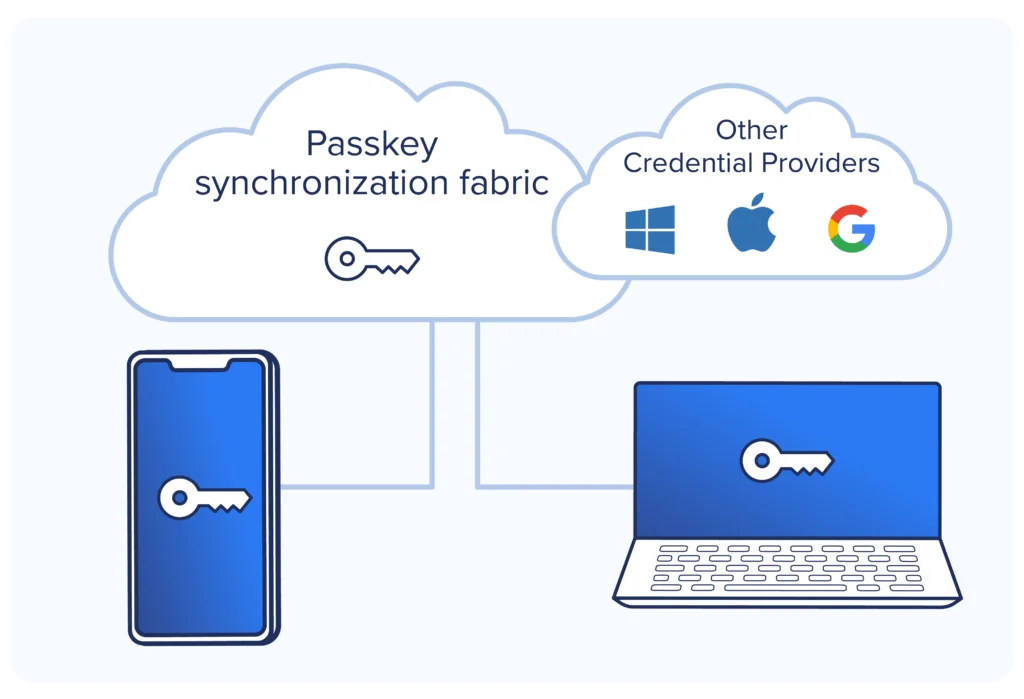
A software version of FIDO2 became viable in 2022, when Apple, Google, and Microsoft jointly announced support for a FIDO passwordless standard called ‘passkey.’ Up to that point, FIDO was delivered as hardware security keys in the form of self-contained USB plugin-style tokens supplied by Yubico, Fatiran, and other hardware vendors.
Alternatively, passkey are managed by platform providers like Apple, Google, and Microsoft and are designed to sync across multiple user devices within the same vendor ecosystem. They provide a similar level of passwordless experience and security as the hardware FIDO2 tokens but without the expense or overhead of hardware. As a result, passkeys have gained traction with the consumer-facing side of enterprise user access. However, due to the nature of software passkey sharability and lack of other assurance capabilities, they have not gained traction in enterprise workforce use cases.
Then In 2023, the FIDO Alliance extended the passkey name to refer to any type of FIDO credential and created subcategories of passkey for their functionality. Two categories have now been established to distinguish the characteristics of synced passkey and device-bound passkey:
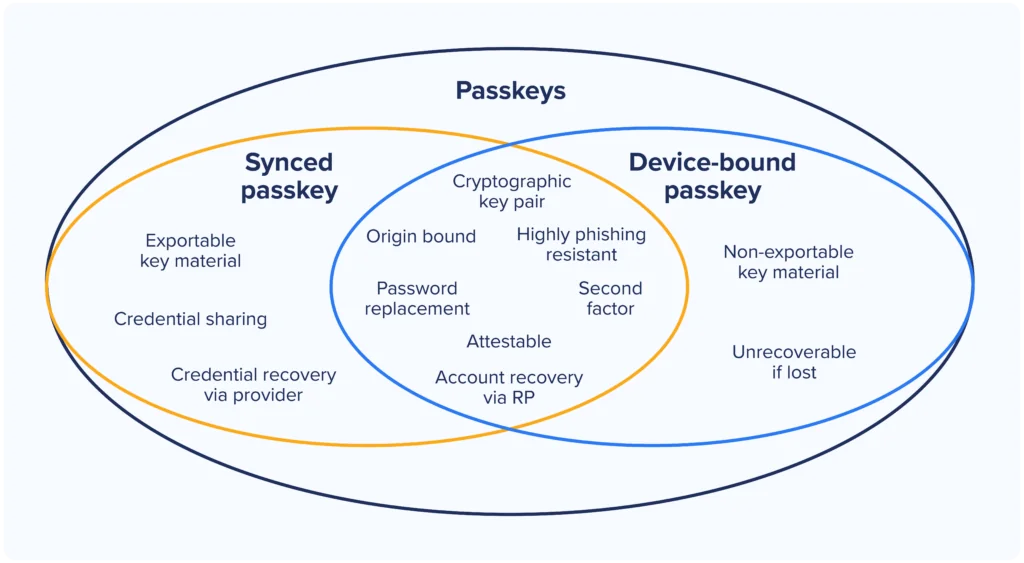
Device-bound passkey
Previously referred to as FIDO security key or generically as FIDO2 are referred to as device-bound passkey now, a type of passkey bound into a hardware device (e.g., TPM, secure enclave) that can’t be exported. Device-bound passkey characteristics include:
- Found on hardware security keys, smartphones, laptops
- No backup of the private key credential.
- Users must register additional credentials for backup in the case the primary authentication device fails or is missing
- The most secure type of passkey
Synced passkey
A category of passkey that can be backed up and synchronized by a credential fabric provider, such as Apple, Google, and Microsoft. Synced passkey can be shared between users’ devices and between people in the same way that passwords can be shared.
A credential provider might be a platform/OS vendor or third party with a business model similar to a password manager. Characteristics of synced passkey include:
- Software private key credentials are recoverable
- Passkey security in the fabric is the provider’s responsibility, but the user is responsible for usage security
- Generally regarded as the weakest form of passkey, although FIDO recommends using synced passkeys anyway because the same weaknesses exist as with passwords, and passkeys are stronger
How Does FIDO2 Work?
Securing FIDO Authentication with Out-of-Band and Device-Based Methods
One of the key ideas that make FIDO authentication secure is using out-of-band (OOB) methods to authenticate user identities. OOB authentication is especially resilient against smash-and-grab data breaches in which hackers compromise a server and gain access to many user accounts.
FIDO authentication can be performed in hardware or software. Some hardware FIDO keys include a trusted platform module (TPM) to handle user identities. A TPM is a piece of hardware that can store sensitive information, such as private encryption keys, and is resilient against physical tampering. FIDO keys such as Yubico’s Yubikey product line contain secure modules to protect users’ private keys.
FIDO can also be implemented in software through mobile applications as a software token, leveraging the mobile enclave and biometric capabilities of smartphones. Mobile authenticators leverage hardware and security modules that exist on the user’s device, such as facial recognition and fingerprint scanners, to protect the user’s security key.
How does FIDO authentication work
FIDO uses public-key cryptography to provide secure and convenient authentication technologies. For every online account that uses FIDO, there is a public and private key that enables services to validate workers’ identities without relying on users’ knowledge of secrets (passwords) or their ability to recognize a legitimate website when being redirected to a phishing website.
| FIDO authentication | Traditional MFA | |
| Impersonation resistant | ✓ | ❌ |
| Social engineering resistant | ✓ | ❌ |
| Man-in-the-middle resistant | ✓ | ❌ |
Phishing resistant MFA is accomplished during the account setup with the target FIDO-supported application or the SSO identity provider referred to as the Relying Party (RP). Data, including the authenticator public key, is sent to the RP through the WebAuthn protocol to prevent attackers from impersonating a legitimate user. Then the username and Relying Party (RP) URL are exchanged to create a channel binding between the authenticator and the RP to prevent redirection to a fake website during a phishing attack.
How does FIDO use asymmetric cryptography for security?
Over the course of its existence, FIDO has developed several specifications for authentication mechanisms. The specifications can be implemented with a wide variety of technologies such as fingerprint sensors, facial recognition, or hardware tokens.
The fundamental protocol used in all versions of FIDO is asymmetric cryptography. As opposed to symmetric cryptography, where a single key is used for both encryption and decryption, asymmetric cryptography uses separate keys to encrypt and decrypt data.
Asymmetric encryption is the basis for public key infrastructure (PKI), which is used in FIDO authentication technologies. For every user, a public and private keypair gets generated. The public key is stored on the servers of the service provider and used to verify users’ identities and encrypt their information. The private key gets stored on users’ devices or cloud fabric, and used to sign in to authentication challenges and validate users’ identities and decrypt their information. PKI makes sure that even if a hacker breaches the servers of the service provider, they won’t be able to hijack user accounts or access the sensitive information they store.
What Is FIDO attestation?
As stated above, the main difference between synced passkey and device-bound passkey is shareability and recoverability. The other key attribute difference between the two types is attestation. The term refers to a technique built-in to the FIDO and WebAuthn protocols that enables the authenticator to use a cryptographic signing to verify the chain of trust from the device’s manufacturer.
Synced passkeys do not support attestation while device-bound passkeys do. These three characteristics of synced passkeys hinder their adoption in the enterprise workforce use cases.
How does the FIDO enrollment process work?
When the user signs up with a FIDO-enabled service, the following happens:
- After users fill out the registration form, the service asks them to choose a FIDO authenticator of their choice. This can be a FIDO-compliant authenticator app or a security key or a TPM.
- Once the user specifies her authenticator, the FIDO device generates a cryptographic keypair.
- The device sends the public key to the service, which registers it in its user database and associates it with each user’s account.
- The private key and other sensitive information such as fingerprint scans and facial data never leave the user’s device.
How does the FIDO authentication process work?
When users want to log in to a FIDO-enabled service, the following happens:
- The user presents herself by providing a username or email.
- The service presents a cryptographic challenge.
- The user uses her FIDO authenticator app or key to sign the challenge.
- After signing the challenge, the user sends the signed challenge back to the server.
- The server verifies the response with the user’s corresponding public key, and if successful, gives the user access to the account.
The interesting fact in the FIDO authentication process is that the server and client exchange no secrets. The main secret information, which is the user’s private key, remains on the device the whole time.
How does FIDO certification work?
FIDO’s certification program determines the compliance and level of security of different services and applications. This is important because it ensures interoperability across different applications and services and also provides important criteria to communicate the level of reliability that each service offers.
Product vendors that become certified by FIDO receive a badge that confirms the integrity and interoperability of their products with FIDO’s specifications. For instance, a FIDO2-certified server will be able to operate with any FIDO2-certified authenticator, even if the two products have been developed by different companies.
FIDO has different certification programs that conform to various levels of involvement in creating authentication servers, applications, and hardware.
The Functional Certification program is an end-to-end process that allows organizations to validate the compatibility and interoperability of their products and services with FIDO specifications. The process involves self-testing tools and verification by FIDO experts. After going through the process and getting their products approved, organizations can file to receive a certified logo which they can print on their packaging and publish on their websites.
Authenticator vendors can also register the metadata of their products on FIDO’s servers to facilitate interoperability with other FIDO-enabled products.
What are the FIDO certification levels?
Certified FIDO authenticators are classified on different levels, which specify their level of security:
- Level 1: This includes all software and hardware authenticators that implement the FIDO2, UAF, or U2F specification. This is the most basic implementation of FIDO authenticator and protects users against phishing, server breaches, and man-in-the-middle (MitM) attacks.
- Level 2: Certified authenticators must have extra security measures that protect security keys against more advanced attacks. Level 2 authenticators are resilient to malware that might want to extract information by gaining access to the device’s operating system.
- Level 3: FIDO authenticators protect the user’s keys against basic hardware attacks. The device should be resistant against physical tampering or at least show clear signs if a hacker manipulates the device’s hardware.
- Level 3+: The most secure type of FIDO authenticator, Level 3 authenticators must store their keys in a TPM which prevents any type of physical tampering or data extraction methods.
FIDO authentication with biometric certification for security and reliability
With biometric authentication becoming a convenient, secure, and affordable option on many devices, vendors are becoming more inclined to offer it to their clients. However, the sensitivity of implementing biometric authentication and handling biometric data has created complexities in verifying vendors’ products.
FIDO’s biometric authentication certification program is meant to provide a baseline to verify the security and reliability of biometric authentication technologies. FIDO’s Biometric Certification is a requirement for any FIDO authenticator with a biometric component. However, biometric authenticator vendors who don’t apply for a FIDO Authenticator Certification can still have their technology evaluated and certified for FIDO’s Biometric Certification.

Enterprise FIDO adoption challenges
Workforce use case coverage gaps
FIDO is great because it is phishing-resistant and simplifies worker login workflows. But as the protocol name WebAuthn implies, FIDO only works for web apps. However, Enterprises are much more than web apps that can be easily made ready for FIDO.
By adding other IAM technologies, like Windows Hello for Business (WHfB) with Entra ID to your identity infrastructure, FIDO can be extended to Windows machine login and a few more Microsoft things (see diagram below). Unfortunately, for most enterprises, that isn’t enough for their whole enterprise (see use case coverage diagram above).
In many cases, use case coverage gaps involve the company’s most sensitive enterprise data, often stored on-prem and often the ultimate targets of attackers. As a result, users have to know and use their directory passwords to access unsupported apps and services, leaving the password and associated phishing risk in place.
Complicated user experience
FIDO use case gaps create a solution based on “sometimes passwordless” rather than achieving the goal of a passwordless enterprise where users never create, remember, or type passwords. With FIDO, workers get frustrated with multiple login workflows, some accesses with FIDO, others with passwords. Less frequently used passwords create more risk because they’re easier to forget, have to be simple to remember, and have to be written down. As a result, users and IT still have to manage password resets that often involve Help Desk calls.
Fallback to passwords
The third area of FIDO for workforce challenges surrounds businesses’ need for work continuity. It is inevitable that a worker will leave behind their authenticator, lose it completely, or break it.
At that point, businesses must have a fallback mechanism in place to continue work production. FIDO provides the mechanism for a second, third, or nth FIDO authenticator to be added to the RP, but that creates additional expense and complexity. For most businesses, the fallback is to leave passwords login as an option for login. In these scenarios, the security risk persists.
How does the Octopus platform extend FIDO across the enterprise?
Like other passwordless MFA solutions that aim to stop phishing, the Octopus Authentication Platform supports FIDO2 to secure web application access. But unlike other passwordless methods, we also extend the benefits of passwordless MFA – and the FIDO approach – enterprise-wide.
That includes delivering FIDO login for Macs and Linux servers, VPNs (which generally use Radius protocols), and LDAP-based systems on-premises. The Octopus platform covers the full range of enterprise use cases, including using FIDO authentication for on-prem and legacy password-based apps without redesign.

The Octopus Authentication Platform is built around a patented technology called Invisible Secret Rotation. The platform replaces the user’s directory password entry with an ephemeral machine-generated token that the Octopus manages and rotates. The user never knows that the token exists or when it gets rotated.
Instead, users authenticate to Octopus using strong methods like FIDO2, passkey, smartcards, and phishing-resistant mobile push through the Octopus Desktop-to-App pinning technology. Once the user has passed the high-assurance authentication, Octopus orchestrates access to user desktops, SSO, remote services, and password-based apps without passwords.
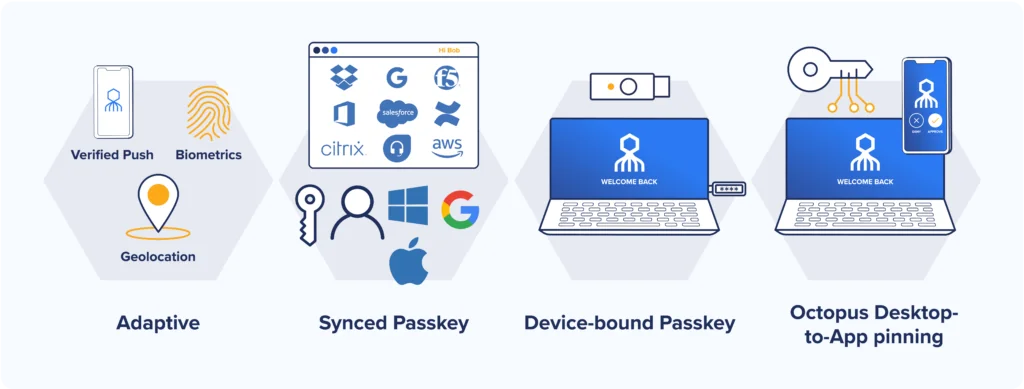
This ephemeral token approach makes Octopus compatible with existing enterprise applications and directory infrastructure without redesign. This compatibility saves businesses time and expenses in achieving their zero-trust identity posture goals.
Summary
FIDO is clearly the future of high-assurance passwordless authentication. The FIDO Alliance continues to evolve the technical and business capabilities of passkey authentication to broaden passkey capabilities. Today, passkey limitations and incompatibility with existing enterprise infrastructure limit its ability to expand rapidly as a complete workforce authentication solution.
However, by combining passkey with the Octoupus Platform, enterprise-wide high-assurance FIDO authentication can be achieved.
Key takeaways
- FIDO Authentication aims to reduce reliance on passwords by using secure, passwordless methods.
- Asymmetric encryption, public key infrastructure (PKI), and channel binding are foundational to FIDO Authentication’s security.
- Octopus and FIDO Alliance are driving the transition to a more secure, passwordless future for online and enterprise-wide authentication.