By promoting the security benefits of Windows Hello for Business (WHfB), Microsoft helped educate enterprise security leaders about the value of a passwordless user login process. Today’s cyber criminals mount a wide range of automated attacks on user credentials that factor into more than 80% of breaches each year. Getting rid of the vulnerable password avoids substantial risk and streamlines the login process to deliver a better user experience (UX).
But every approach to multi-factor authentication (MFA) has its pros and cons including WHfB. For the enterprise, the biggest detractor to Windows Hello is that the solution only works for Microsoft Windows applications, and only for a portion of those. Most enterprises use a whole lot more.
We’ll take a quick look at why passwordless for Microsoft matters, the benefits and limitations of WHfB and what it takes to bridge the gap between the coverage delivered by Microsoft’s “free” Passworldess login and the phishing-resistant MFA enterprises actually need.
Passwordless MFA stops phishing
Regulators, cyber insurance carriers, and cybersecurity authorities such as CISA, NIST, and MITRE ATT&CK all stress the need for strong authentication to stop ransomware and safeguard remote access. Nearly all specify using MFA and some set the bar even higher by requiring MFA to be phishing-resistant.
That’s where passwordless comes in since removing credentials from the process means there’s nothing to phish. But that’s not the only criteria.
Whatever approach your company takes to stop phishing, coverage must extend to all applications everywhere you do business, be it on-premises, from home, in the cloud, and in locations where verifying identity proves challenging. Your MFA solution also must address a wide range of use cases including remote and shared access.
Doing all of this without creating additional complexity—and risk—calls for a unified approach that Windows Hello and other proprietary solutions fail to deliver.
Stronger security and a better UX
A patchworked approach to user authentication makes it easier for intruders to sneak in and lurk within your environment undetected. That gives hackers time to scope things out for a while before beginning lateral movement toward your high-profile assets. A unified login workflow improves detection, incident response, and prevention, particularly in hybrid environments that support third-party access.
But that’s not all. A unified passwordless approach to authentication also saves users considerable time and effort and relieves them out of the tedious burden of managing secrets—passwords—and juggling authenticators like USB drives, smartcards, and hardware tokens. By our calculations, a unified passwordless login can save the average user 15-20 minutes per day making them 5% more productive over time.
The more and more quickly you onboard applications to a centrally managed MFA solution, the greater your efficiency gains become.
Enterprises aren’t just Windows
Not even Microsoft. Recent statistics show Windows accounts for less than 70% of all installed operating systems. That means that, even if WHfB could secure all Windows-powered PCs, most enterprises would still have significant gaps in coverage.
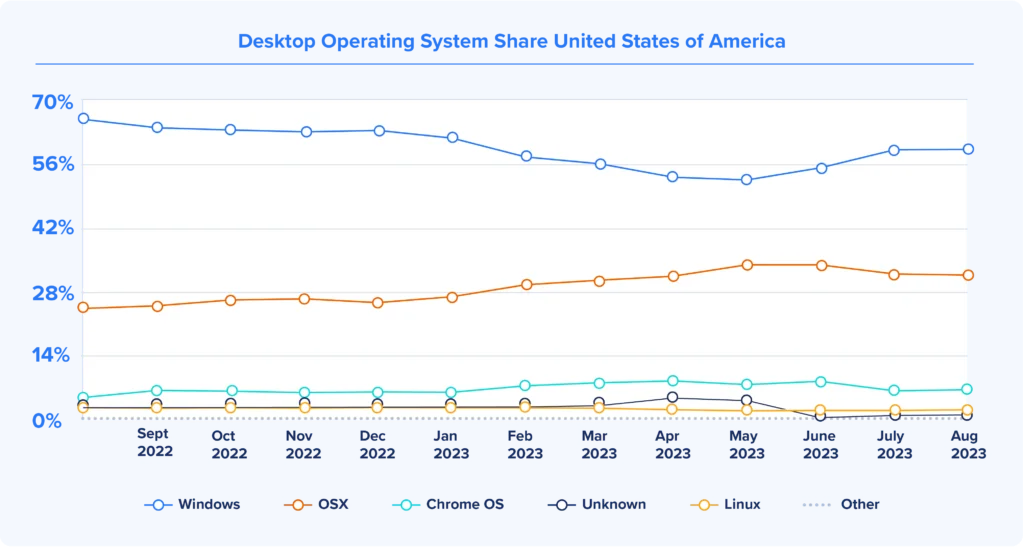
Macs used by executives and Linux machines used by IT and engineering represent prime targets for spear phishing, whaling and other focused, carefully orchestrated attacks.
Octopus delivers the industry’s broadest workforce Passwordless MFA coverage
In contrast to WHfB, the Octopus passwordless MFA platform delivers high-assurance, phishing-resistant MFA for Windows, Macs, Linux servers, VPNs, and LDAP-based systems on-premises.
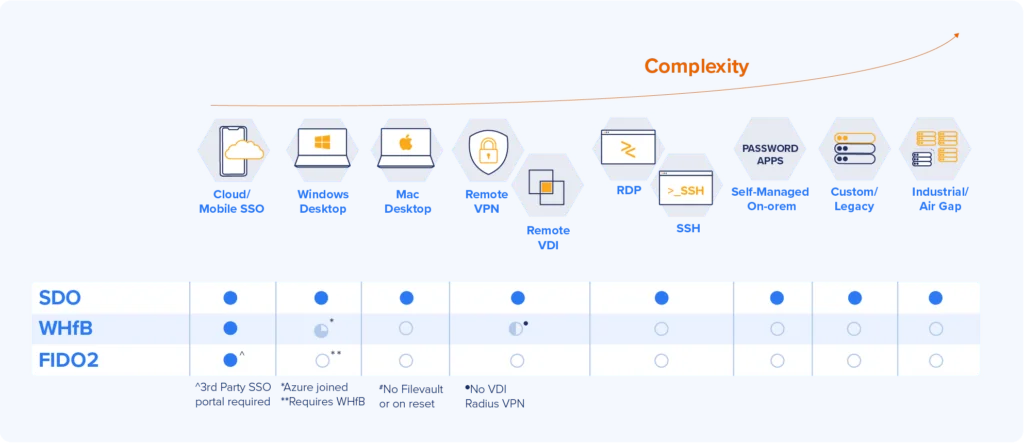
“Hello” won’t open all your Windows
Windows Hello doesn’t address the full spectrum of most enterprises’ Microsoft applications and services, either. For example, WHfB doesn’t work with popular virtual private network (VPN) technologies and services such as Remote Desktop Protocol (RDP) and RADIUS. Many requests from remote users still connect in through VPNs that require transactions to cross the public Internet where threat actors lay in wait.
As hackers continue to target VPN, TechRadar writes:
SSL and TLS can be exploited. Worse still, some of these weaknesses have carried through to VPNs that use them, particularly ones where hackers can gain access to authentication credentials like the private keys used to secure VPNs.
This flaw highlights how a passwordless VPN enhances remote access security by eliminating credentials—provided your MFA integrates with your VPN. Securing the corporate VPN ranks at the top of most CISO’s priority lists and you can’t check this box with Windows Hello.
Limited support for biometrics
Many customers like the convenience of using biometrics—for example, touching their finger to a home screen—to log into devices. Windows Hello does support biometrics, but in some cases can only store biometric recognition data for ten users per machine. That makes the technology unsuitable for many enterprises, universities, healthcare facilities, and critical infrastructure (CI) providers where multiple users require access to the same machines.
In most use cases the current fallback would be to keep using passwords, an especially bad idea for shared devices. Conversely, a unified passwordless approach helps to secure shared workstations while avoiding collusion and insider attacks.
Octopus delivers what Windows Hello can’t: a secure, unified login experience
The leaders at Secret Double Octopus built our passwordless MFA platform around three basic principles:
- Removing user passwords and user password management stops phishing
- To achieve phishing resistance, the platform must be able to make all authentication workflows phishing-resistant
- MFA should make logging in easier for users—and where possible—for IT
The Octopus platform accelerates the enterprise passwordless journey by enabling IAM leaders to achieve the benefits of passwordless MFA across their entire IT infrastructures — without changing their IT infrastructures. SDO uses FIDO-compliant cryptography to secure web applications with strong authentication. We added our own advanced cryptography to deliver the same security benefits and greater ease-of-use on-premises and in challenging physical locations.
Octopus passwordless MFA works for any workforce application, even those that are inherently password-centric. And we save IT time by not requiring apps and directories to be retooled or rearchitected.
High assurance with mobile push—an industry-first
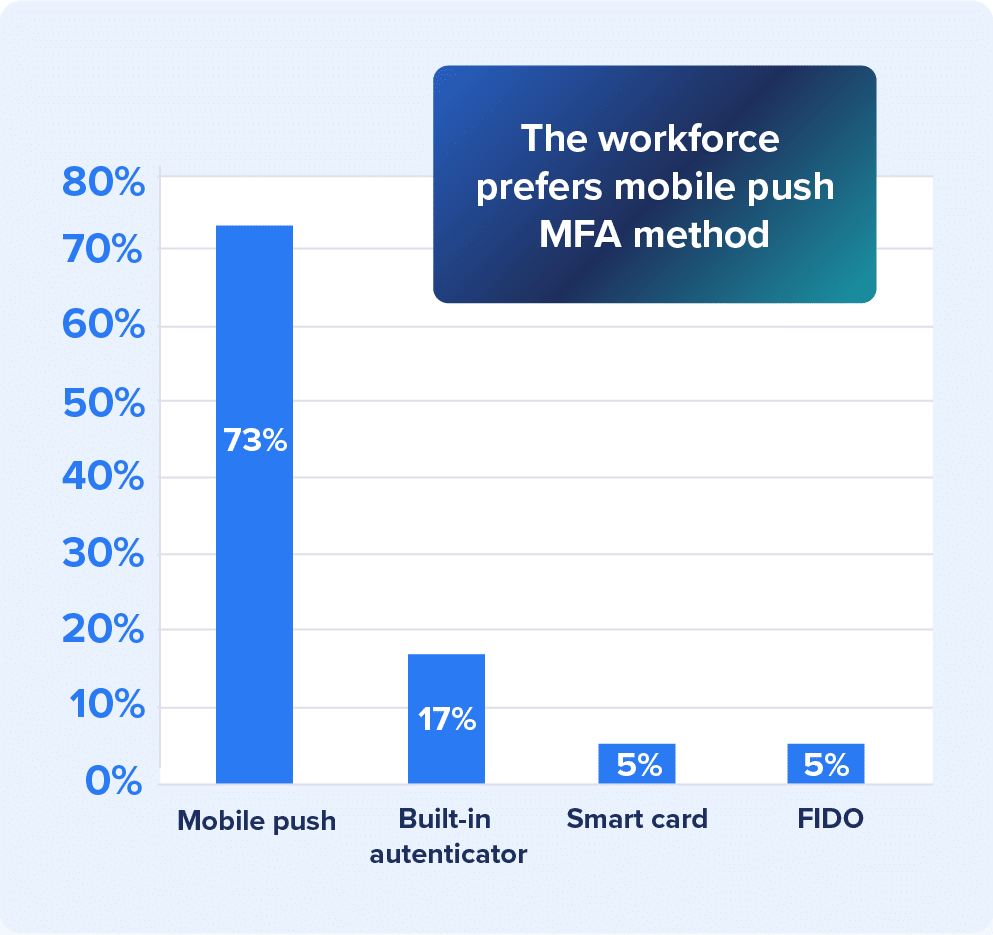
Users prefer the convenience of mobile push and biometrics. But even with push notifications adding a second factor to authentication, MFA isn’t secure enough to be considered “high assurance” by industries facing the strictest requirements. Here, Octopus elevates mobile push to the level of High Assurance using cryptographic key pairs and a first-of-its-kind new feature.
SDO’s Proximity Assurance capability requires users to be within range of the workstations they’re attempting to sign onto and to complete authentication using both a PIN sent via push and a biometric.
Sometimes you need good push. With Octopus, businesses with the highest assurance MFA requirements—finance, CI, healthcare, etc. – can use high assurance mobile push with other NIST 800-63B AAL3-conforming hardware authenticators.
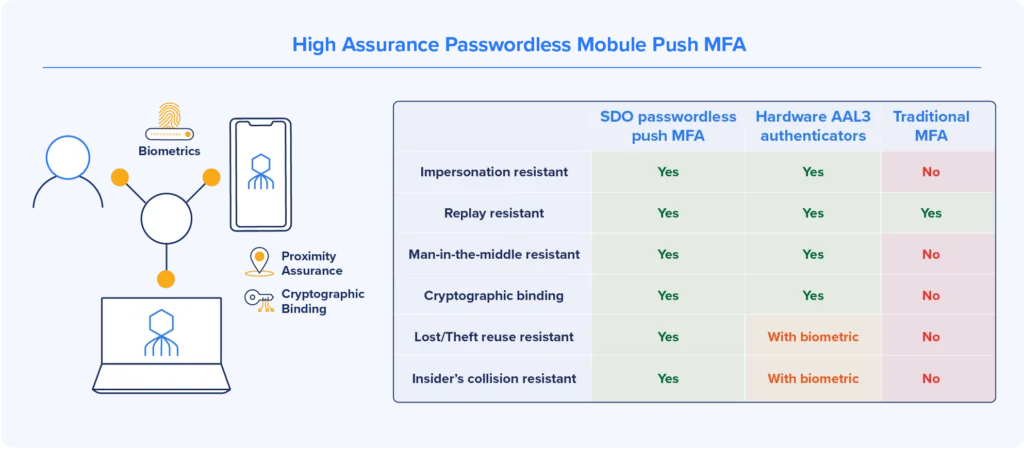
This authentication workflow combines “what users have”—the right device—with “who users are” (verified using their fingerprint, voice, or iris) to create high-assurance passwordless multi-factor verification. This approach delivers greater assurance than passwords, regular SMS-based texts, and other techniques based on “what users know.”
Best-in-class versus best-in-suite
While bundled Microsoft security suites protect a huge percentage of enterprise desktops, there’s a lot to be said for choosing an MFA solution from an identity management leader. In September, SDO announced its selection as a 2023 SINET 16 Innovator, an award based solely on merit and the importance of the company’s vision and innovation.
Most important, the award attests to growing recognition of the need for passwordless MFA to secure the modern workforce. The vendor- and technology-agnostic Octopus platform uniquely secures any and all workforce users and applications, on the web or on-prem, and anywhere else the business might take place.
Learn more, start now
For more information on our passwordless MFA solution, watch this short video to learn how you can get started in about an hour. Or, run an ROI calculation on our Passwordless ROI Calculator to see how much you can save within the first year.